Tor: An Overview
What is Tor?
At first glance, the Tor network is similar to a VPN. Messages to and from your computer pass through the Tor network rather than connecting directly to resources on the Internet. But where VPNs provide privacy, Tor provides anonymity.
A VPN service can keep outsiders from seeing where you go and what you do on the Internet, but there are ways to defeat the privacy they give you. By its nature, a VPN service has access to information about you. You have to trust them to protect that information.
When you use the Tor network you don’t have to trust anyone. The design of Tor makes you virtually anonymous when you go online. While no system is 100 percent foolproof, it would be exceedingly difficult for anyone to identify you when you use the Tor network.
Is Tor a VPN?
Since both Tor and VPNs perform similar functions, you might wonder, “Is Tor really just a specific type of VPN?” The answer is, “No.” Here’s why:
A VPN is a network of servers that protects your privacy by encrypting your messages and hiding your IP address. Your VPN provider controls both the VPN software on your computer, and the servers in their network. You have to trust your VPN service to protect your privacy when you use their network.
Tor is a network of servers that you communicate with anonymously. No one organization controls both the Tor software on your computer and the individual servers in the network. You don’t need to trust anyone to use Tor safely. As much as anything else, the fact that you don’t need to trust anyone when you use Tor is what makes it distinct from a VPN.
How Does Tor Work?
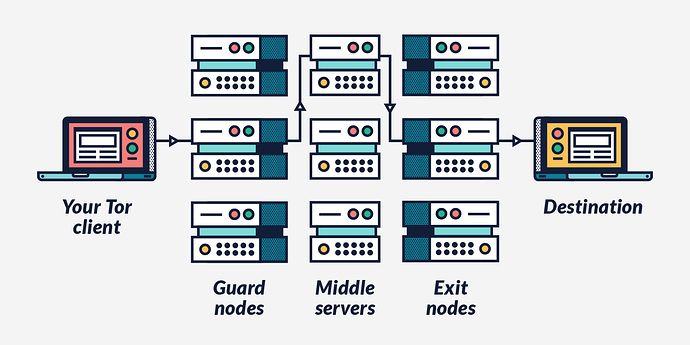
The Tor network is designed so that no server can know both who you are and what you do. The network consists of thousands of independent servers run by volunteers around the world. Here’s what happens when your computer wants to send a message using the Tor network:
- Software on your computer (either the Tor browser or another Tor-enabled program) selects three Tor servers at random . The software then builds a path between those three servers.
- The process starts with the server that will connect to the public Internet (called the Exit Node ). The Tor software on your computer encrypts the message in a way that only the Exit Node can decrypt.
- The software then repeats this process with the server in the middle. Now the message is encrypted twice .
- The software does the same with the server that will first receive the message from your computer (called the Guard Node ). Now the message is encrypted three times .
- Once the message is encrypted, the Tor software on your computer sends the encrypted message to the Guard Node. This server removes the outermost layer of encryption. The Guard Node cannot read the original message because there are still two layers of encryption . However, the software includes the address of the next server in the path when it encrypts the message.
- The Guard Node sends the message to the server in the middle of the path . This server removes the second layer of encryption. Like the first computer it still can’t read the message because there is one more layer of encryption . But removing this layer of encryption tells it the address of the Exit Node.
- The middle server sends the message to the Exit Node . The Exit Node removes the final layer of encryption . This means the Exit Node can see your original message. However, because the message was relayed through the other servers in the path, the Exit Node doesn’t know who sent the message.
This is key to understanding Tor so let’s look at what each server in the path knows.
- The Guard Node can see the IP address of your computer. But it doesn’t know what the message says because of the additional layers of encryption. So all the Guard Node knows is that your computer sent a message using Tor and that it needs to forward that message to the middle server .
- The middle server knows the message came from the Guard Node and that it has to forward the message to the Exit Node. It can’t read the message because there is one layer of encryption left . The middle server doesn’t know who sent the message to the Guard Node because that information isn’t passed through the Tor network.
- The Exit Node knows what the message says because it has to peel off the final layer of encryption before the message can go out to the public Internet. But it doesn’t know where the message came from originally. All it knows is that the middle server forwarded the message.
No one server knows or can know both where the message came from and what it says. This is how Tor provides anonymity.
Tor Onion Routing vs. VPN Encryption
The way messages are routed within their networks is another key difference between VPNs and Tor.
When you send a message with a VPN, the message gets encrypted on your computer and sent to a specific server in the VPN network. There, it is decrypted and forwarded to the final destination. Messages coming to your computer get sent to the VPN server. There they are encrypted and sent to your computer. The VPN software on your computer decrypts the message. Once you establish a VPN connection, you continue to use the same server for the duration.
Tor uses Onion Routing, a more complex approach. Onion Routing requires the message to pass through at least three, randomly-selected Tor servers before it gets sent to its final destination. Before the message leaves your computer, the Tor software encrypts the message multiple times. The effect is to give the message layers of encryption that must be peeled, similar to layers of an onion.
As the message passes through the network, each server decrypts one of the layers. When the final server in the path peels away the final layer of encryption, it exposes your original message, and forwards it to its destination outside the Tor network.
As a result of the encryption and the way Tor servers pass messages between each other, none of the three servers can know both who sent the message, and what the message says. This makes you anonymous within the network. To further protect against bad actors trying to hack the network, the Tor software in your computer chooses new server to use approximately every 10 minutes.
Tor Advantages
Using Tor to connect to the Internet offers several advantages over an unprotected connection.
Difficult to shut down
Because it is made up of thousands of servers scattered around the world, Tor is very difficult to shut down. The network is distributed, not centralized. That means there is no headquarters, corporate office or main server to attack.
Most Tor servers are run by volunteer privacy advocates. To shut down Tor, you would have to go after each individual server in the network. This makes trying to shut down Tor about as practical as stopping P2P music transfers or shutting down Bitcoin.
Nearly complete anonymity
There are ways Tor can be attacked, but the people of the Tor Project are constantly working to make Tor safer. While no person or network can guarantee you 100 percent anonymity, Tor provides you much more online anonymity than even the best VPN.
Tor Disadvantages
While Tor is a great system for using the Internet anonymously, it isn’t a perfect solution. Here are some disadvantages to using Tor.
Very slow
Messages in the Tor network go through three (or more) widely-dispersed servers and get encrypted and decrypted at least three times. As a result, the Tor network is very slow. Using it to stream videos or for peer-to-peer file sharing would be very difficult.
Run by volunteers
Because the Tor network is run by volunteers, there’s no built-in source of money to pay for maintaining and upgrading the network. Some servers in the network are old and slow, or have bad Internet connections. Additionally, there is always the risk that the volunteers running the network aren’t trustworthy.
Low device compatibility
The Guardian Project maintains Tor on Android devices. Currently, the Tor Browser is not available for iOS, meaning you can’t use it on your iPhone or iPad.